Catharsis Market Wiki -- The Comprehensive Darknet and Anonymity Encyclopedia
Welcome to Catharsis Market Wiki, the most thorough and continuously updated knowledge base dedicated to the darknet ecosystem, digital anonymity, and operational security. Whether you are a researcher studying underground networks, a journalist investigating censorship-resistant publishing, a privacy advocate defending civil liberties, or simply a curious individual trying to understand the hidden layers of the internet, this wiki serves as your authoritative reference point. Every article published here is written with technical accuracy, neutrality, and an educational focus that prioritizes factual depth over sensationalism.
The modern internet is a vast construct, yet the portion most people interact with daily -- the clearnet, indexed by search engines like Google and Bing -- represents only a fraction of all networked content. Beneath this visible layer lies the deep web, encompassing databases, private intranets, academic repositories, and paywalled publications that search engine crawlers cannot reach. Deeper still exists the dark web, a subset of the deep web accessible only through specialized software such as the Tor Browser or the I2P network. These overlay networks were engineered specifically to provide anonymity, circumvent censorship, and protect the identities of their users through layered encryption and decentralized routing.
Catharsis Market Wiki exists to document, explain, and contextualize the technologies, platforms, and practices that define this hidden internet. Our mission is strictly educational. We do not facilitate illegal activity, nor do we endorse any criminal enterprise. Instead, we provide the same caliber of technical documentation you would find in an academic cybersecurity curriculum or a professional penetration testing handbook -- applied to the darknet domain.
Understanding the Darknet Landscape
The term "darknet" often conjures images of illicit marketplaces and criminal forums, but this narrow portrayal ignores the technology's legitimate and vital uses. The Tor Project, originally developed by the United States Naval Research Laboratory, was designed to protect intelligence communications. Today, Tor is used by millions of people worldwide, including journalists operating in authoritarian regimes, whistleblowers exposing government corruption, domestic violence survivors hiding from abusers, and activists organizing under repressive governments.
The Electronic Frontier Foundation (EFF) has long advocated for the right to anonymous speech and the preservation of privacy-enhancing technologies. Organizations like Freedom of the Press Foundation operate SecureDrop instances as Tor hidden services, allowing sources to submit documents to news organizations without revealing their identity. The United Nations has recognized anonymity and encryption as fundamental to freedom of expression in the digital age.
Within this landscape, darknet marketplaces represent one of the most studied phenomena. These platforms operate as anonymous e-commerce sites, utilizing cryptocurrency for payments and onion routing for network-level anonymity. Understanding how these markets function -- their escrow mechanisms, dispute resolution systems, vendor reputation frameworks, and security architectures -- provides valuable insight into decentralized trust systems, cryptographic commerce, and the socioeconomic forces driving underground economies.
Our wiki covers this entire spectrum without bias. From the technical underpinnings of onion routing to the practical steps of setting up a hardened operating system, from the history of Silk Road to the cryptographic fundamentals of PGP encryption, every topic is treated with the depth and rigor it deserves.
Featured Articles
Our knowledge base contains in-depth guides covering every critical aspect of darknet navigation and digital privacy. These featured articles represent the core curriculum for anyone seeking to understand anonymity technology.
- The Complete Tor Browser Guide -- A comprehensive walkthrough of the Tor Browser, covering installation, configuration, security settings, bridge relays, pluggable transports, and common pitfalls that compromise anonymity. This guide draws on official Tor Project documentation and real-world threat scenarios.
- PGP Encryption: From Theory to Practice -- Master Pretty Good Privacy encryption, the cornerstone of secure communication on the darknet. Learn key generation, key management, message signing, verification, and the Web of Trust model that underpins PGP's decentralized identity system.
- Tails OS: The Amnesic Incognito Live System -- Everything you need to know about Tails, the Debian-based live operating system designed to preserve privacy and anonymity. Covers USB installation, persistent storage encryption, software configuration, and operational security practices unique to Tails.
- OPSEC Fundamentals for the Digital Age -- Operational security is the discipline that separates the protected from the exposed. This article covers threat modeling, attack surface reduction, compartmentalization, behavioral patterns, and the common OPSEC failures that have led to high-profile arrests.
- How Onion Routing Works -- A deep technical explanation of onion routing, the protocol that powers the Tor network. Understand circuit construction, relay selection, cell encryption, directory authorities, and the cryptographic handshakes that establish anonymous connections.
- Monero and Cryptocurrency Privacy -- Bitcoin is pseudonymous, not anonymous. Learn why Monero (XMR) became the preferred cryptocurrency for privacy-conscious users, and understand ring signatures, stealth addresses, RingCT, and Dandelion++ propagation.
Recent Guides and Tutorials
We continuously expand our library with practical, hands-on guides that address both foundational concepts and advanced techniques. These recently published or updated resources cover some of the most requested topics in the privacy and security community.
- Whonix Setup Guide: Isolating Your Traffic -- Whonix provides workstation isolation by routing all traffic through a dedicated Tor gateway virtual machine. This guide covers VirtualBox and KVM installation, network configuration, and the security advantages of Whonix's split architecture over single-system Tor usage.
- Linux Security Hardening -- Transform a standard Linux installation into a fortress. Covers kernel hardening parameters, mandatory access control with AppArmor and SELinux, filesystem encryption, firewall configuration with iptables and nftables, and audit logging.
- Browser Fingerprinting Defense -- Your browser reveals far more than your IP address. This guide explains canvas fingerprinting, WebGL fingerprinting, AudioContext fingerprinting, font enumeration, and the countermeasures implemented by Tor Browser and other privacy tools.
- DNS Privacy and Encrypted DNS -- DNS queries are one of the most overlooked privacy leaks. Understand DNS-over-HTTPS (DoH), DNS-over-TLS (DoT), DNSCrypt, and how to configure system-level encrypted DNS resolution to prevent ISP surveillance and DNS manipulation.
- Secure Messaging Applications -- A comparative analysis of encrypted messaging platforms including Signal, Session, Briar, and Ricochet Refresh. Evaluates each platform's encryption protocol, metadata protection, decentralization, and suitability for different threat models.
- Metadata Removal: Erasing Your Digital Footprints -- Every file you create or share carries hidden metadata that can reveal your identity, location, and device information. Learn to strip EXIF data from images, sanitize documents, and use tools like MAT2 and ExifTool to eliminate these invisible traces.
The Technology Behind Anonymity
True anonymity on the internet does not happen by accident. It requires a deliberate combination of software, protocols, and behavioral discipline working in concert. At the network level, the Tor protocol encapsulates user traffic in multiple layers of encryption, passing it through a series of volunteer-operated relays distributed across the globe. Each relay in the circuit peels away one layer of encryption, learning only the address of the previous and next hop, never the full path. This architecture, known as onion routing, makes it computationally infeasible for any single observer to correlate a user's origin with their destination.
Beyond Tor, the I2P (Invisible Internet Project) network provides an alternative approach to anonymous communication. While Tor is optimized for accessing the clearnet anonymously through exit nodes, I2P is designed primarily as a self-contained network of hidden services called "eepsites." I2P uses garlic routing -- a variant of onion routing that bundles multiple encrypted messages together -- and unidirectional tunnels that separate inbound and outbound traffic, making traffic analysis significantly more difficult.
At the application level, operating systems like Tails and Whonix provide pre-configured environments that force all network traffic through Tor, preventing accidental IP leaks. Tails runs entirely from a USB drive or DVD, leaves no trace on the host computer, and wipes its RAM on shutdown. Whonix takes a different approach, using two virtual machines -- a gateway that handles all Tor routing and a workstation that is completely network-isolated except through the gateway -- ensuring that even if the workstation is compromised, the user's real IP address cannot be discovered.
Encryption forms the third critical pillar. PGP (Pretty Good Privacy) provides end-to-end message encryption and digital signatures, allowing users to communicate securely and verify each other's identities without relying on centralized certificate authorities. On the darknet, PGP is not optional -- it is the standard for encrypted communication between market users, for verifying the authenticity of market URLs, and for signing messages to prove identity.
Video Resource: Understanding Tor and Online Anonymity
The following video from Computerphile provides an excellent introduction to how Tor works and why it matters for internet privacy. Understanding the fundamentals of onion routing is essential before diving deeper into the technical guides available on this wiki.
For additional visual learning resources, the Computerphile channel covers numerous topics relevant to our wiki, including public key cryptography, VPN security, and browser fingerprinting. We also recommend Mental Outlaw and The Hated One channels for in-depth privacy and security content.
Essential External Resources and Tools
The privacy and anonymity ecosystem is supported by a constellation of open-source projects and advocacy organizations. The following resources are indispensable references for anyone serious about digital security.
- The Tor Project -- The official home of the Tor network and Tor Browser. Download the latest browser, read the official documentation, and learn about volunteer relay operation.
- Privacy Guides -- A community-driven resource recommending privacy-respecting tools and services. Covers VPNs, email providers, browsers, operating systems, and encryption software with transparent evaluation criteria.
- Whonix -- The official Whonix documentation wiki, providing exhaustive guides on installation, configuration, and the security model behind Whonix's isolated virtual machine architecture.
- Tails -- The official Tails website with download links, installation instructions, and documentation for the amnesic live operating system that routes all connections through Tor.
- EFF Privacy Resources -- The Electronic Frontier Foundation's privacy section, offering legal analysis, advocacy updates, and practical guides like Surveillance Self-Defense (SSD).
- GitHub Privacy Tool Repositories -- GitHub hosts thousands of open-source privacy tools. Notable repositories include cryptocurrency tools, document sanitization, and networking utilities.
Open-Source Privacy Tools on GitHub
The open-source community has produced remarkable tools for digital privacy. These GitHub repositories represent some of the most important projects in the ecosystem:
- torproject/tor -- The core Tor daemon source code. Written primarily in C, this repository contains the implementation of the onion routing protocol, circuit construction logic, and relay software.
- Signal Protocol -- The Signal messaging protocol, which provides end-to-end encryption with forward secrecy and deniable authentication, is open-source and has been independently audited.
- monero-project/monero -- The official Monero repository containing the CryptoNote-based privacy coin implementation with ring signatures, stealth addresses, and RingCT.
- MAT2 (Metadata Anonymisation Toolkit) -- A Python tool for removing metadata from files, supporting images, PDFs, office documents, and more.
- OnionShare -- An open-source tool for securely and anonymously sharing files, hosting websites, and chatting using the Tor network. Developed by Micah Lee of The Intercept.
Darknet Marketplaces: A Scholarly Perspective
Darknet marketplaces have been the subject of extensive academic research across disciplines including criminology, economics, computer science, and public health. These platforms function as decentralized e-commerce ecosystems that rely on cryptographic trust mechanisms rather than legal frameworks. Understanding their operation provides insight into alternative economic models, decentralized governance, and the practical applications of privacy technology at scale.
The Market section of this wiki provides a comprehensive overview of how darknet marketplaces evolved from the original Silk Road to the sophisticated multi-signature escrow platforms operating today. We examine the technological innovations these markets have introduced -- including PGP-verified vendor identities, cryptocurrency escrow systems, and dispute resolution mechanisms -- as well as the law enforcement operations that have targeted them.
For a detailed historical perspective, our History of the Dark Web article traces the evolution of anonymous networks from early cypherpunk mailing lists and USENET through the development of Freenet, Tor, and I2P, and the subsequent emergence of hidden services that would become the backbone of darknet commerce.
Quick Links and Navigation
Catharsis Market Wiki is organized to serve readers at every level of expertise. Use the following quick links to navigate to the section most relevant to your interests.
- Full Article Index -- Browse all 16 in-depth articles organized by category, including Privacy, Security, Networks, and Tools.
- Mirror Sites and Verification -- Learn about mirror sites, how to verify authentic URLs using PGP signatures, and why mirrors are essential for darknet platform availability.
- Market Overview -- Comprehensive documentation of darknet marketplace architecture, security models, and historical evolution.
- Threat Modeling Guide -- Before choosing any tools or techniques, start with threat modeling. Understand who your adversary is, what they can observe, and what you need to protect.
- VPN No-Logs Policies -- Evaluate VPN providers' logging claims, understand jurisdictional considerations, and learn why a VPN alone is insufficient for true anonymity.
- I2P Network Guide -- Explore the Invisible Internet Project as an alternative to Tor, with its unique garlic routing protocol and self-contained eepsite ecosystem.
Why This Wiki Exists
The internet is increasingly surveilled, censored, and commercialized. Governments around the world deploy deep packet inspection to monitor citizen traffic. Internet service providers sell browsing histories to advertisers. Social media platforms harvest behavioral data at industrial scale. In this environment, the ability to communicate privately, access information freely, and transact without surveillance is not merely a convenience -- it is a fundamental human right affirmed by the Universal Declaration of Human Rights (Article 12) and the International Covenant on Civil and Political Rights (Article 17).
Privacy-enhancing technologies like Tor, strong encryption, and anonymous operating systems are the technical enforcement mechanisms for these rights. Without them, the legal guarantees of privacy are hollow. Catharsis Market Wiki documents these technologies so that the knowledge necessary to exercise digital privacy remains accessible, accurate, and free.
We encourage all readers to start with our Threat Modeling Guide to establish a clear understanding of their security needs before exploring specific tools and techniques. Effective privacy is not about using every tool available -- it is about using the right tools for your specific situation, consistently and correctly.
Explore the wiki, deepen your understanding, and take control of your digital footprint. Knowledge is the first line of defense.
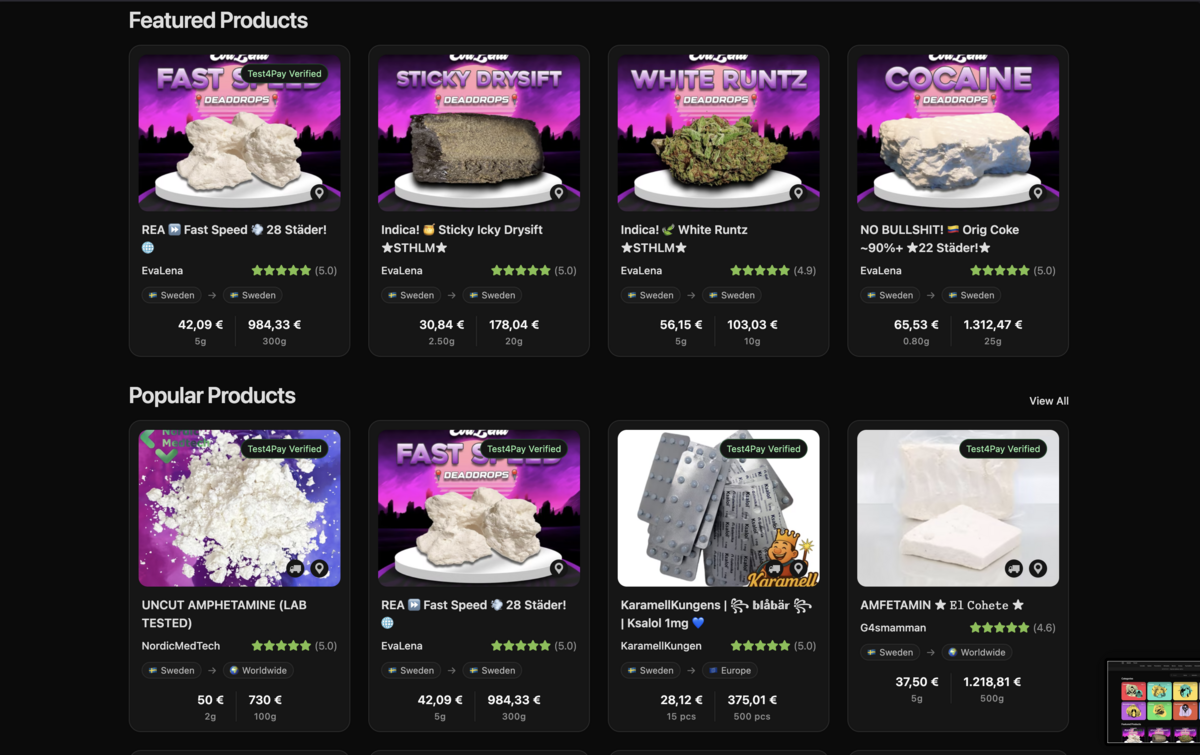
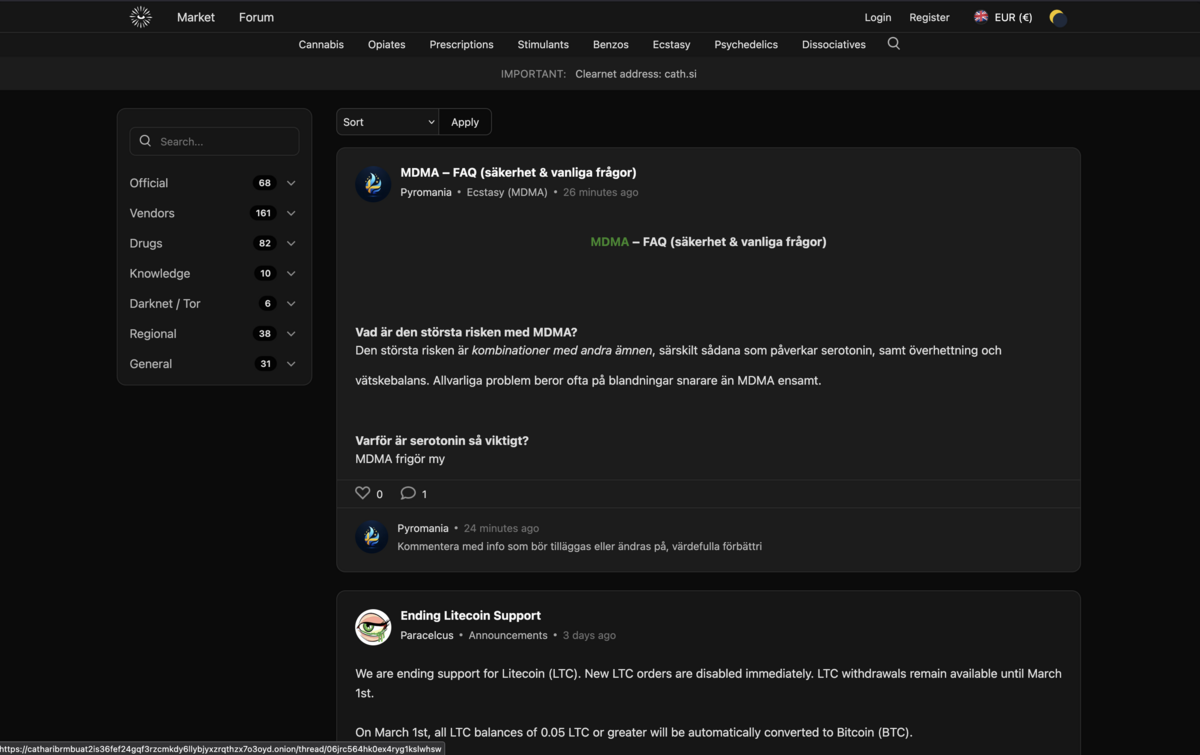
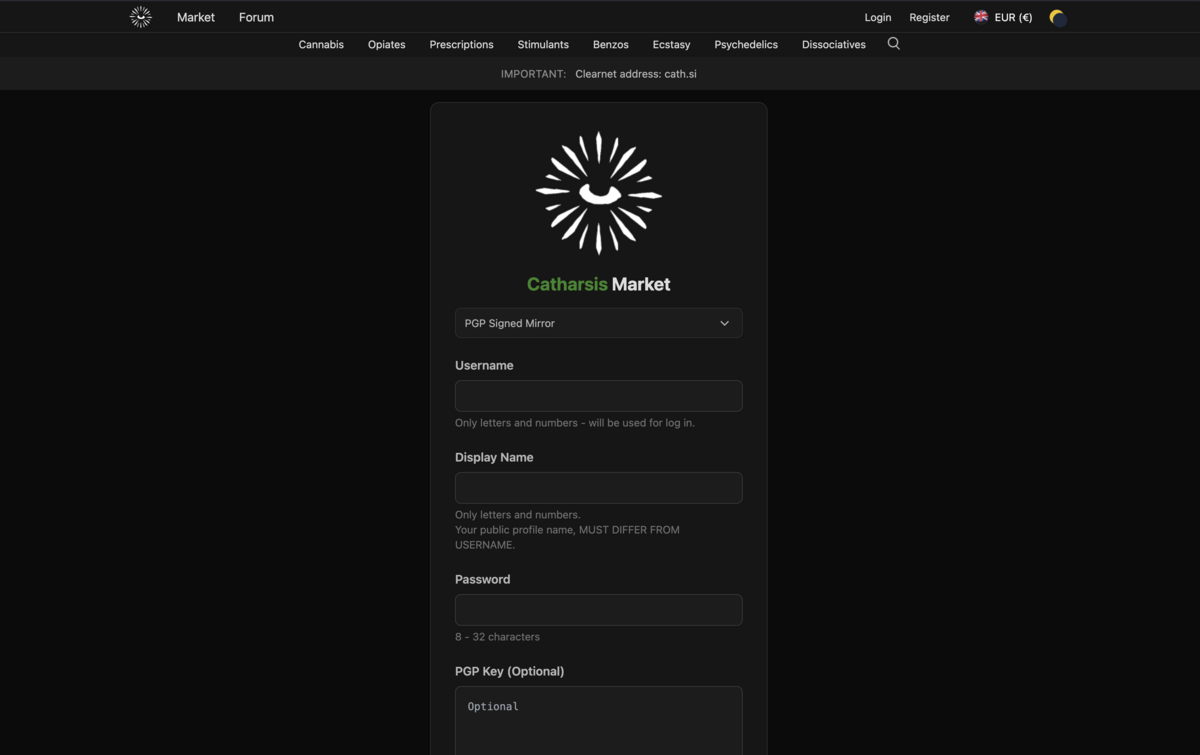
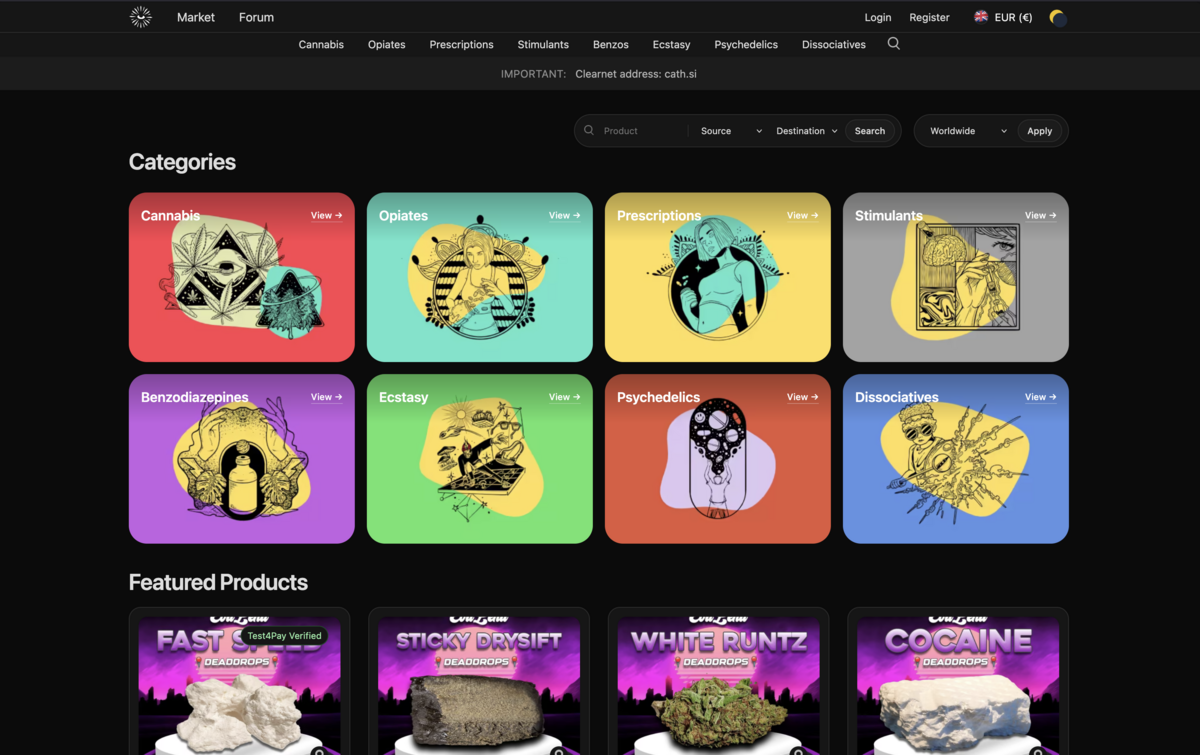
Platform Gallery
Visual overview of the Catharsis Market platform interface, including the marketplace, forum and authentication screens.